Orbital Cybersecurity: NZ Is No Longer Just a Consumer


What NCSC-NZ's co-authorship of the five-nation LEO satcom security standard means for boards with satellite dependencies
One hour before Russian tanks crossed into Ukraine on 24 February 2022, a cyberattack struck a satellite operations network in Germany. The target was not a satellite. It was the ground segment controlling ViaSat's KA-SAT service. Within minutes, approximately 80,000 modems across Europe stopped responding. Ukrainian government communications went dark. German wind farms lost remote monitoring. French law enforcement lost connectivity.
Not a single satellite was physically touched. The attackers went for the ground.
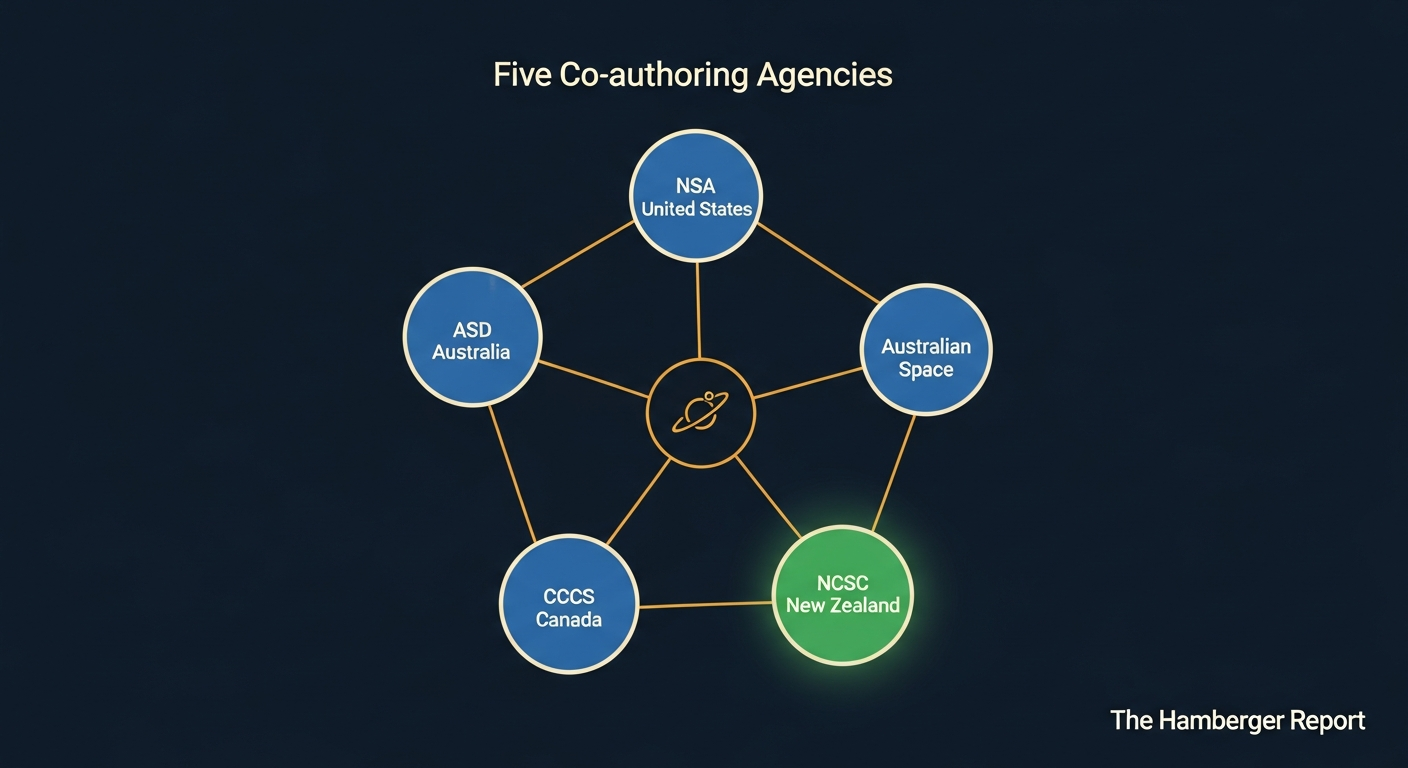
That is the operational pattern that five allied governments documented in a joint Cybersecurity Information Sheet published on 24 March 2026. The document is titled "Securing Space: Cyber Security for Low Earth Orbit Satellite Communications." The authoring agencies are the Australian Signals Directorate's Australian Cyber Security Centre, the Australian Space Agency, the Canadian Centre for Cyber Security, the National Security Agency, and the New Zealand National Cyber Security Centre.
NCSC-NZ is not cited as a contributor, an endorser, or a distribution recipient. It is a named co-author on a primary intelligence document.
If your organisation depends on satellite connectivity, that distinction matters more than the technical content of the document itself.
What the Document Actually Says
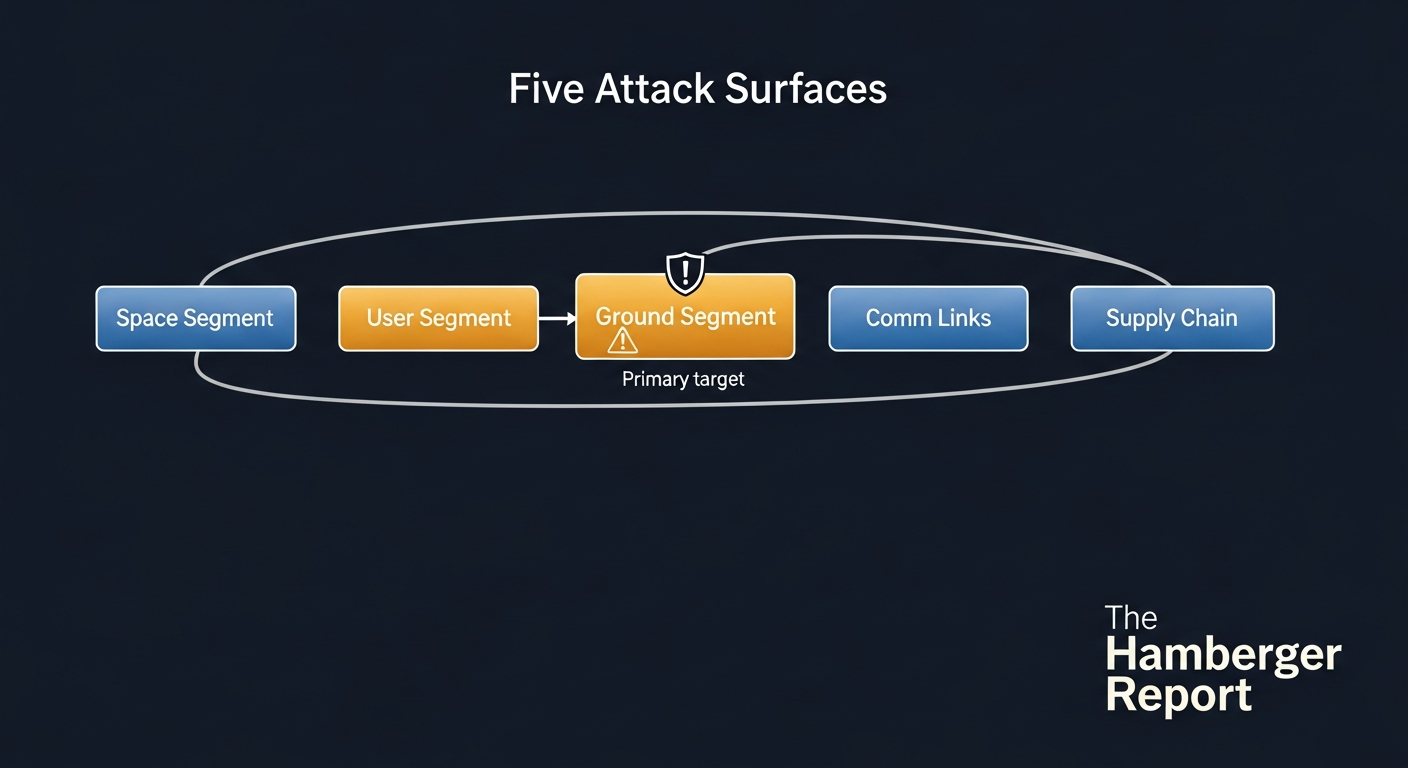
The joint Cybersecurity Information Sheet (CSI) maps risks and countermeasures across five architectural segments of LEO satcom systems.
The space segment covers the satellites themselves. Threats include jamming, unauthorised command injection, payload hijacking, firmware tampering, signal spoofing, and malware injection. The primary mitigation is consistent encryption and authentication across the satellite's operational lifetime, plus a Software Bill of Materials (SBOM) for both satellite and ground-segment software requested from providers.
The ground segment covers control centres, ground stations, gateways, and user terminals. This is the primary soft target. SpaceX runs approximately 50,000 collision avoidance manoeuvres in the Starlink fleet every six months; the satellites are not where the vulnerability lies. The operations networks, ground stations, and user terminals are. The ViaSat 2022 attack demonstrated this with precision.
The user segment covers end-user devices and interfaces. Threats include credential compromise and man-in-the-middle interception on the user-to-satellite link.
The communication links segment addresses the radio-frequency channels susceptible to jamming, spoofing, and interception. LEO satellites move constantly across ground station coverage arcs; the handover moment between stations is a window that adversarial actors can exploit.
The supply chain segment covers the full hardware and software chain for LEO satcom systems. The CSI requests SBOM from providers and expects secure-by-design development practices throughout.
This is a technically grounded, practically applicable document. Its recommendations map directly onto procurement decisions, vendor management obligations, and board-level risk questions. But its production origin is the more significant signal.
The Co-authorship Signal
The governance argument at the centre of Space Mafia begins with an uncomfortable observation: the governance vacuum in orbital AI is the most dangerous single condition in the emerging space economy. "Build the rules before the rockets launch" is the book's closing imperative.
The CSI is evidence that at least five allied governments are acting on that imperative in real time, and that New Zealand is at the table when those rules are written.
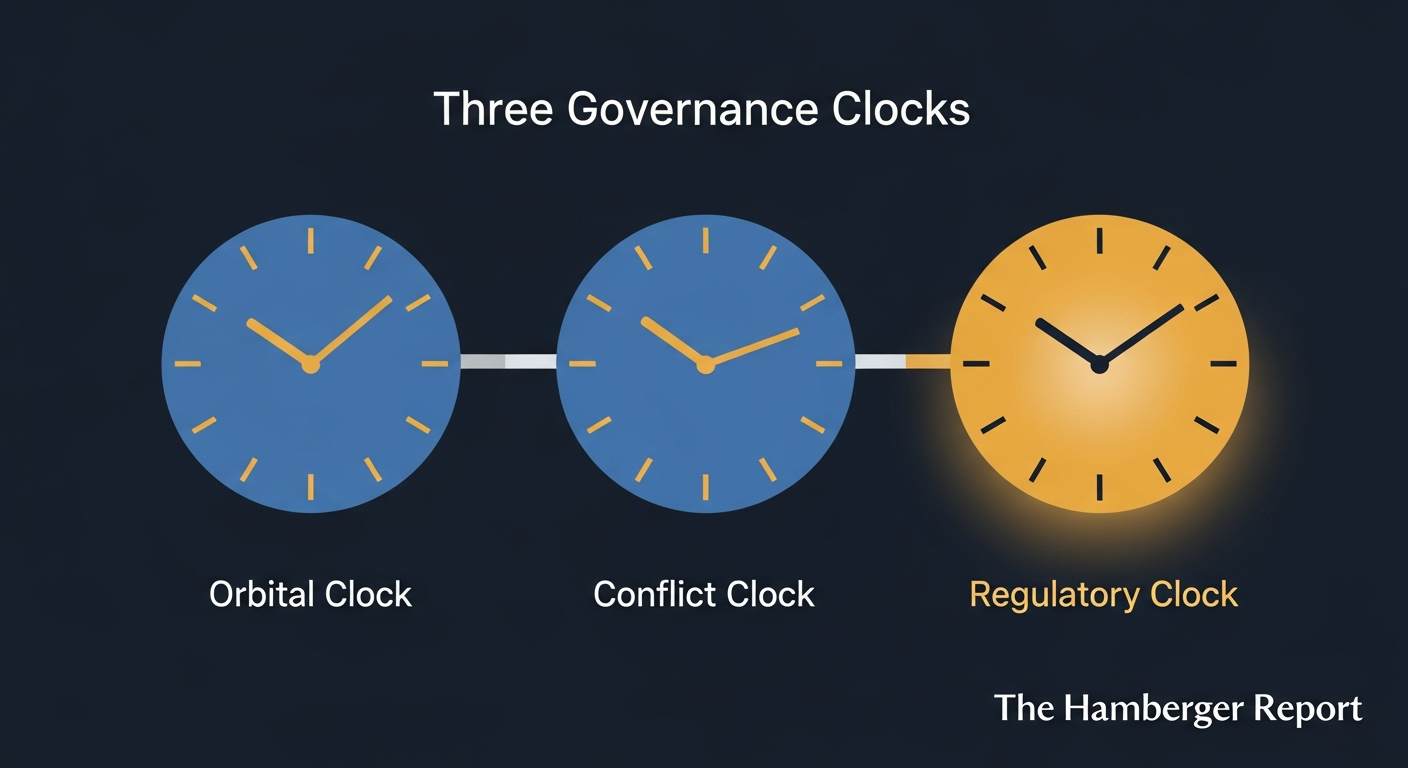
The Space Mafia Three Clocks framework identifies three independently running timers that define the governance action window. The Orbital Clock measures debris accumulation and the approach of Kessler cascade thresholds. The Conflict Clock measures geopolitical deterioration and the acceleration of adversarial-state orbital capabilities. The Regulatory Clock measures the pace at which governance frameworks are being built.
The 24 March 2026 CSI is a Regulatory Clock event. Allied governments are building governance faster than debris accumulates and faster than the Conflict Clock advances. That is the optimistic reading of the data. It is also the correct one.
This is not the first joint intelligence product where NCSC-NZ appears as a named authoring agency. The joint product cadence, which previously focused on terrestrial enterprise IT security, has now extended to orbital infrastructure. Each product in this sequence represents the Regulatory Clock gaining on the Orbital and Conflict Clocks.
Five nations co-authoring a joint security standard for orbital infrastructure is not a routine publication event. It is a distributed, accountable, peer-based security architecture operating in real time. Episode 7 of this series introduced the concept of Collaborative Vertical Integration when examining how Rocket Lab's allied-nation model, spanning launch, spacecraft, propulsion, optical communications, and defence, provides a governance-aligned alternative to single-entity monopoly at the industrial level.
The NCSC-NZ CSI co-authorship is the security governance expression of that same structural commitment. Distributed authority. Mutual accountability. No single point of control or failure.
That structure is what the Heaven pathway looks like in practice.
Under the Skynet pathway, orbital infrastructure governance collapses into opacity, regulatory arbitrage, and capture of the commons by actors with no accountability to any national framework. The Adversarial Kardashev trajectory accelerates when governance frameworks are absent: state and non-state actors exploiting orbital infrastructure for coercive leverage rather than civilian benefit. The ViaSat attack was not an anomaly. It was a preview of what adversarial ground-segment targeting looks like at operational scale, and it preceded what the book's Adversarial Kardashev analysis identifies as the next escalation level: persistent disruption of LEO satcom infrastructure as a standard instrument of statecraft.
The CSI names this threat environment explicitly. So does the trajectory.
The Constellation Scale Problem
There is a reason this advisory appeared when it did.
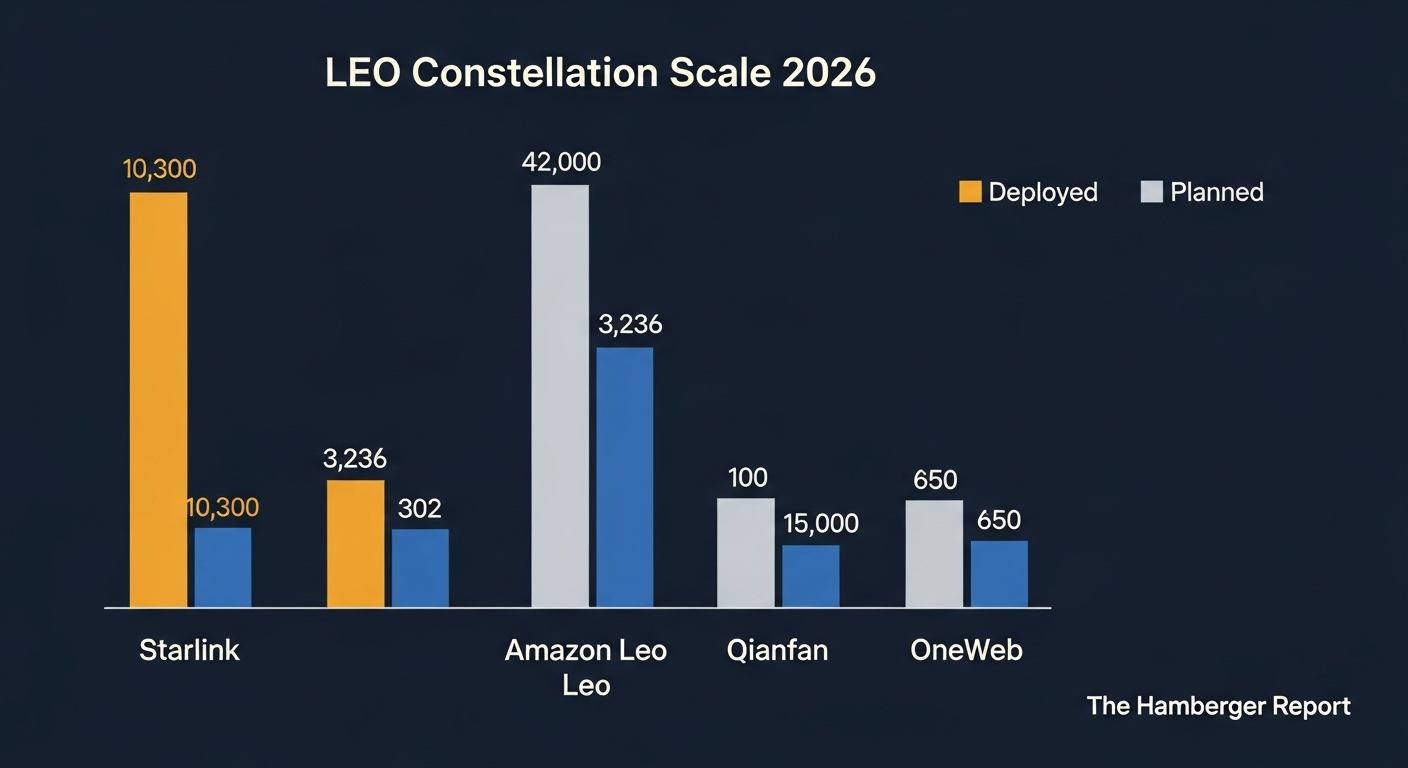
The LEO satcom landscape has changed materially in the past eighteen months. Starlink now operates more than 10,300 deployed satellites, with regulatory approval for approximately 15,000 and applications filed for up to 42,000. Amazon Leo, rebranded from Project Kuiper in November 2025, has deployed 302 satellites of a planned 3,236, with consumer services targeted for mid-2026. China's Qianfan constellation has more than 100 satellites deployed of a planned 15,000. OneWeb operates approximately 650 satellites, repositioned for enterprise and government clients.
A 2025 RAND analysis projected approximately 25,000 satellites on orbit by 2031, with roughly 70 per cent operated commercially. The governance architecture for those constellations is being assembled right now. There is no existing treaty framework adequate to the scale of the task. The Five Country Council joint product line is one of the mechanisms building that architecture piece by piece.
Boards procuring LEO services today are making procurement decisions against a regulatory landscape that is still forming. The CSI represents the current thinking of five allied national security agencies about what secure procurement of those services looks like. A vendor unable to meet this standard is a vendor operating below the threshold that the allied intelligence community has publicly documented.
What This Means for NZ Organisations
New Zealand has a specific regulatory exposure that many organisations have not yet mapped.
The Outer Space and High-altitude Activities Amendment Act 2025 requires registration and compliance from any organisation that operates infrastructure supporting space objects. This includes ground stations, uplink facilities, and user terminals that form part of a LEO satcom service. The compliance deadline is 29 July 2026. Non-compliance carries a fine of NZ$250,000.
An organisation that procures Starlink connectivity for a rural operations facility, and whose terminal forms part of the service network, may qualify as a "space operator" under the Act without having sought that classification. The Hidden Space Operator risk, introduced in Episode 1 of this series, is not theoretical. It is an active compliance gap with a known deadline.
NCSC-NZ's co-authorship of the CSI, and the CSI's specific guidance on ground-segment and supply-chain security, is directly applicable to any NZ organisation assessing its obligations under the Act. The co-authorship establishes that the Act's compliance framework now has an internationally co-authored security standard sitting above it. These are not separate documents. They are the same governance architecture at different layers.
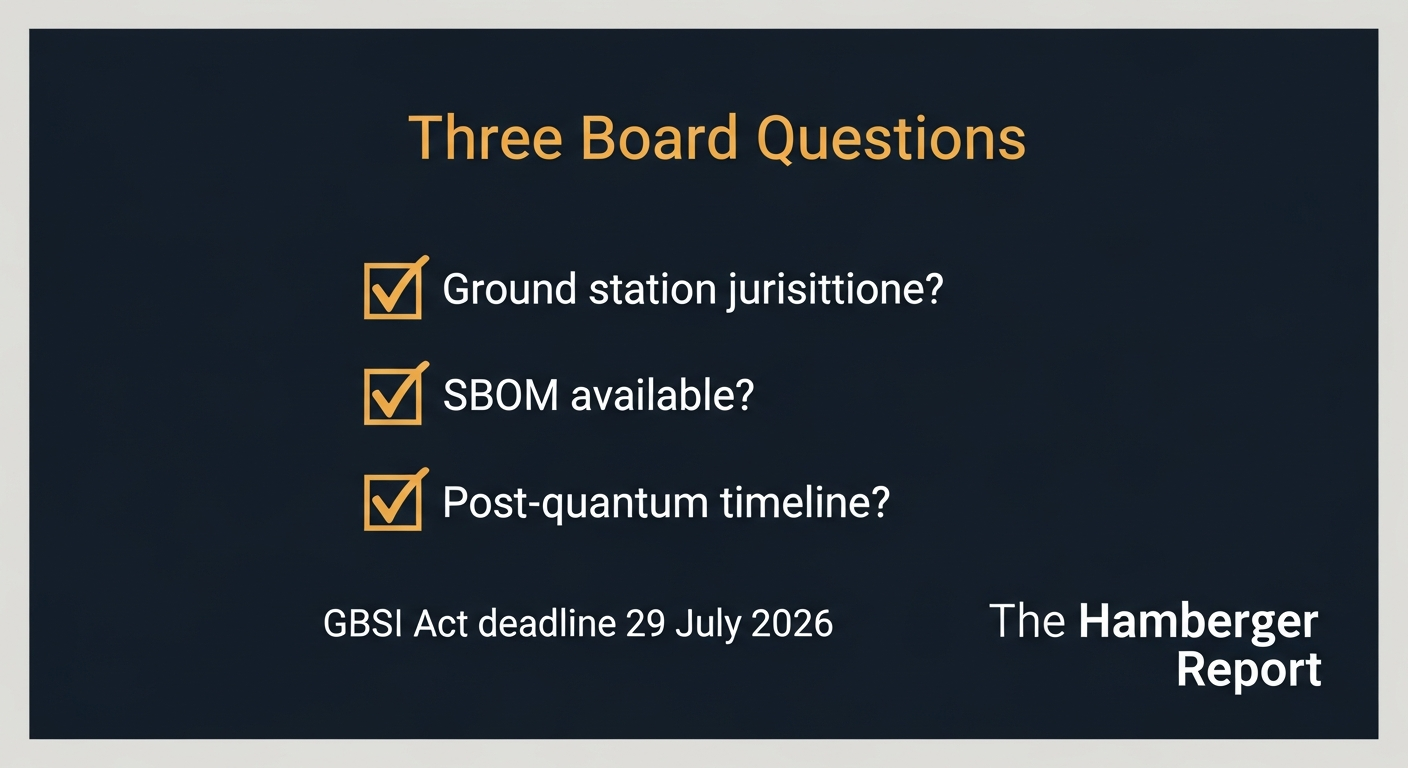
There are three questions every NZ board with LEO service dependencies should put to its providers before the 29 July 2026 deadline.
One: Where are your ground stations, and who has physical access? The ViaSat attack targeted a ground station in Germany. The critical vulnerability in a LEO satcom service is not the satellite; it is physical and cyber security of the ground infrastructure. A provider should be able to confirm the jurisdictions in which its ground stations operate, the security protocols governing physical access, and whether those ground stations are subject to the CLOUD Act or equivalent legislation that would expose NZ-origin traffic to foreign government access.
Two: Can you provide a Software Bill of Materials for ground-segment and satellite software? The CSI explicitly requests this from providers. A provider unwilling to produce an SBOM either does not know its own supply chain or has reasons to obscure it. Neither position is acceptable for an organisation with GBSI Act exposure. SBOM requests are now a standard due diligence item in allied government procurement; NZ boards should apply the same standard.
Three: What is your timeline for post-quantum cryptographic migration across the ground and link segments? Post-quantum migration is underway across allied government systems. The CSI's supply chain guidance encompasses cryptographic standard hygiene. A LEO satcom provider with no defined migration timeline is passing an accumulating cryptographic risk to its clients, and that risk compounds as the handover window problem in LEO link segments is more exposed to harvest-now-decrypt-later attacks than most terrestrial services.
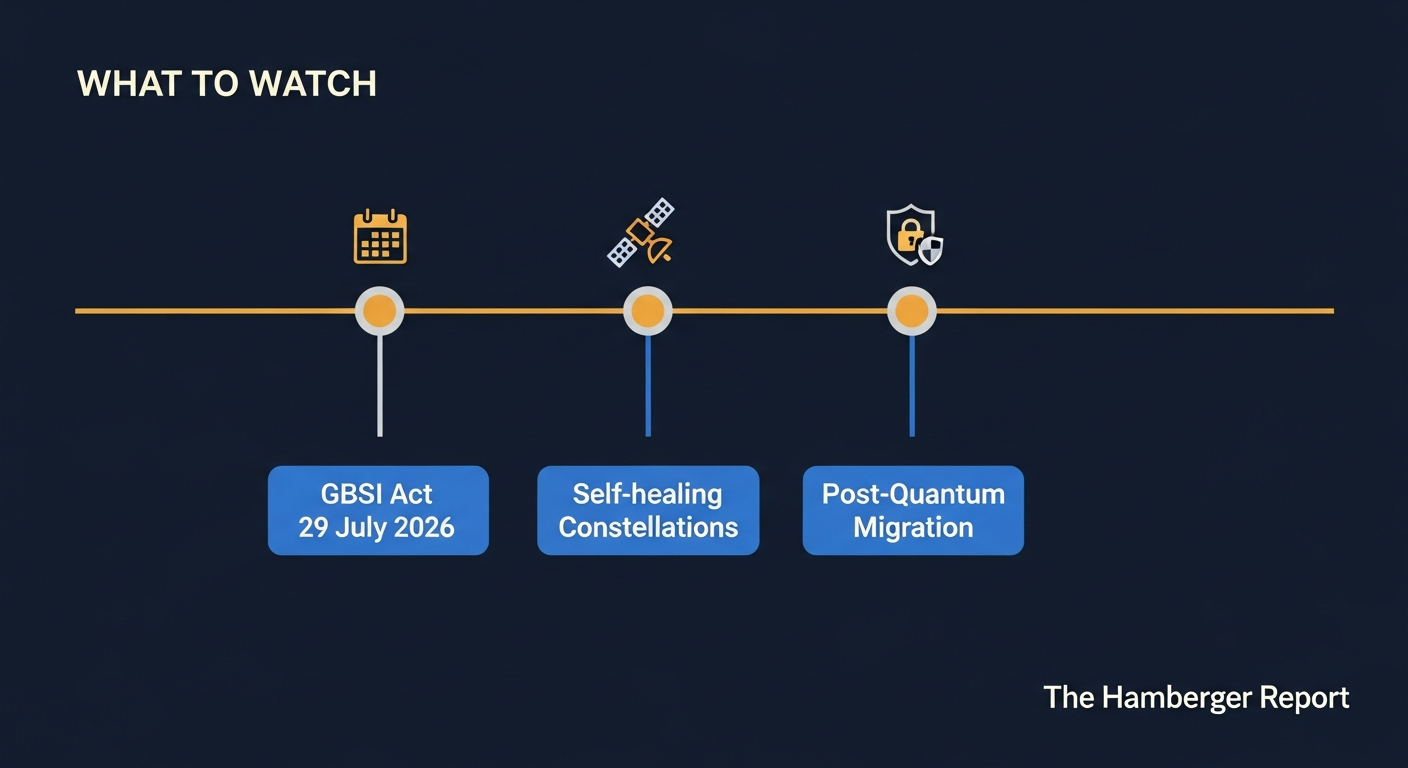
What to Watch Next
The joint product cadence has extended from terrestrial IT into orbital infrastructure. That shift is not cosmetic.
Several developments are worth monitoring over the next six months.
The GBSI Act enforcement window opens on 29 July 2026. Organisations that have not assessed their space operator classification by that date face both regulatory exposure and the operational risk of unregistered infrastructure. The enforcement transition is not a formality; MBIE has signalled active compliance monitoring.
The self-healing constellation pattern is emerging as an operational architecture. Satellites capable of detecting threats autonomously and sharing intelligence with trusted neighbouring satellites in their constellation represent the next frontier of orbital cyber defence. These capabilities are being developed across defence and commercial programmes; the governance frameworks for autonomous machine-to-machine threat response in orbit do not yet exist at adequate scale.
The post-quantum migration timeline across commercial LEO providers is the near-term supply chain watch item. The Linux 7.0 kernel, released 12 April 2026, introduced ML-DSA post-quantum signatures for kernel module authentication. Allied government systems are migrating now. Commercial LEO satcom providers operating with legacy cryptographic standards in their ground and link segments carry an accumulating risk that their enterprise and government clients are inheriting by default.
The joint product line from the Five Country Council will continue. The CSI on LEO satcom security is unlikely to be the last orbital infrastructure advisory in this sequence. NZ's position as a named co-author in this product line is a structural commitment, not a single-publication event.
The Architecture of Accountability
New Zealand has been a passive beneficiary of allied intelligence sharing for most of its digital history. The NCSC-NZ co-authorship of a joint LEO satcom security advisory signals a shift in that relationship. Not because of political intent, but because NZ has developed the institutional capability and the operational depth to contribute to the architecture of the standard itself.
The governance architecture for the orbital era is being built in real time. The window to shape it is open. The Corporate Kardashev trajectory, the Vertical Integration Singularity dynamic, and the Pirate Radio Parallel all describe the same underlying pattern: the exploitation of governance vacuums by actors with the capital and operational presence to move faster than national frameworks.
The CSI is evidence that five nations are choosing not to let that pattern complete itself unchallenged.
The board that does not know this, and has not asked its LEO providers the three questions above, is the board that will be surprised when the compliance window closes on 29 July 2026.
What would change about your organisation's LEO procurement approach if your board treated the NCSC-NZ co-authorship of this advisory as a direct compliance signal rather than a background document? And have you asked your satellite connectivity provider whether it can produce an SBOM?
The views expressed in this article are entirely my own, informed by more than 30 years of professional experience in architecture, security, and technology leadership in New Zealand. They do not represent the views of my employer, any government agency, or the New Zealand government. My commentary on legislation and policy is analytical, drawing on publicly available sources and my professional expertise in architecture, security, and AI governance. I follow the Public Service Commissioner's Code of Conduct for the Public Sector and social media guidance.
Andreas Hamberger is an enterprise architect, security practitioner, and technology strategist with more than 30 years of experience across New Zealand's public and private sectors. He holds TOGAF Practitioner, IAPP, and AMInstD credentials and a Master of Arts in Philosophy and Logic from Humboldt-Universität zu Berlin. He is an Associate Member of the Institute of Directors New Zealand and principal of Te Pono Limited. Space Mafia examines the sovereignty implications of orbital compute infrastructure.
I use AI tools, including Sudowrite, Claude, Perplexity AI, DeepSeek AI, ChatGPT, Grok, Copilot, Openart and Gemini, as deliberate production tools, not ghostwriters. This is consistent with my position: AI amplifies human judgement; it does not replace it. The frameworks, arguments, and editorial decisions in this series are original work. AI accelerated the process. The thinking is mine.
[1] Australian Signals Directorate's Australian Cyber Security Centre, Australian Space Agency, Canadian Centre for Cyber Security, National Security Agency, New Zealand National Cyber Security Centre. "Securing Space: Cyber Security for Low Earth Orbit Satellite Communications." 24 March 2026. https://media.defense.gov/2026/Mar/24/2003902673
[2] National Security Agency. "NSA Joins International Partners to Release Cybersecurity Guidance for Space Systems." Press Release. 24 March 2026. https://www.nsa.gov/Press-Room/
[3] Via Satellite. "Satellite Ground Systems Remain Primary Cyber Target." April/May 2026.
[4] Intelligence Community News. "Five Nations Release LEO Satellite Cybersecurity Advisory." 25 March 2026.
[5] GlobalSecurity.org. "Securing Space: Cyber Security for Low Earth Orbit Satellite Communications." 24 March 2026. https://www.globalsecurity.org
[6] Wikipedia. "Amazon Satellite Internet." Updated 30 April 2026. https://en.wikipedia.org/wiki/AmazonSatelliteInternet
[7] RAND Corporation. Orbital Infrastructure Projections 2025. 2025.
[8] New Zealand Ministry of Business, Innovation and Employment. Outer Space and High-altitude Activities Amendment Act 2025. https://www.legislation.govt.nz/
[9] NCSC New Zealand. "Cyber Security Insights Report, Q3 2025." https://www.ncsc.govt.nz/
[10] Federal News Network / Claroty / Sovada. "US Satellite Cybersecurity Act: OT-Layer Implications." 27 February 2026.
[11] Hamberger, Andreas. Space Mafia: Who Gets to Own Orbital Compute? Te Pono Limited, 2026.
